Businesses, hospitals, and power plants, a country’s infrastructure held hostage. An ultimate covert weapon that can disable defense systems and unravel decades of technological innovation. Cyberwarfare is no longer the stuff of science fiction. Today, we’re facing one of the most potent superweapons of the modern world, and if that doesn’t get your attention, consider that the latest strain can hold your data hostage or delete your files outright.
We’re at war with some bad actors. Last fall the Russians hacked the US Presidential campaign, spreading fake anti-Clinton new stories generated by teams of Russian hackers and amplified by Russian Twitter bots. This summer’s round two is equally insidious. Ransomware is precisely what it sounds like: intrusive software that effectively holds a target’s data hostage unless you pay a ransom.
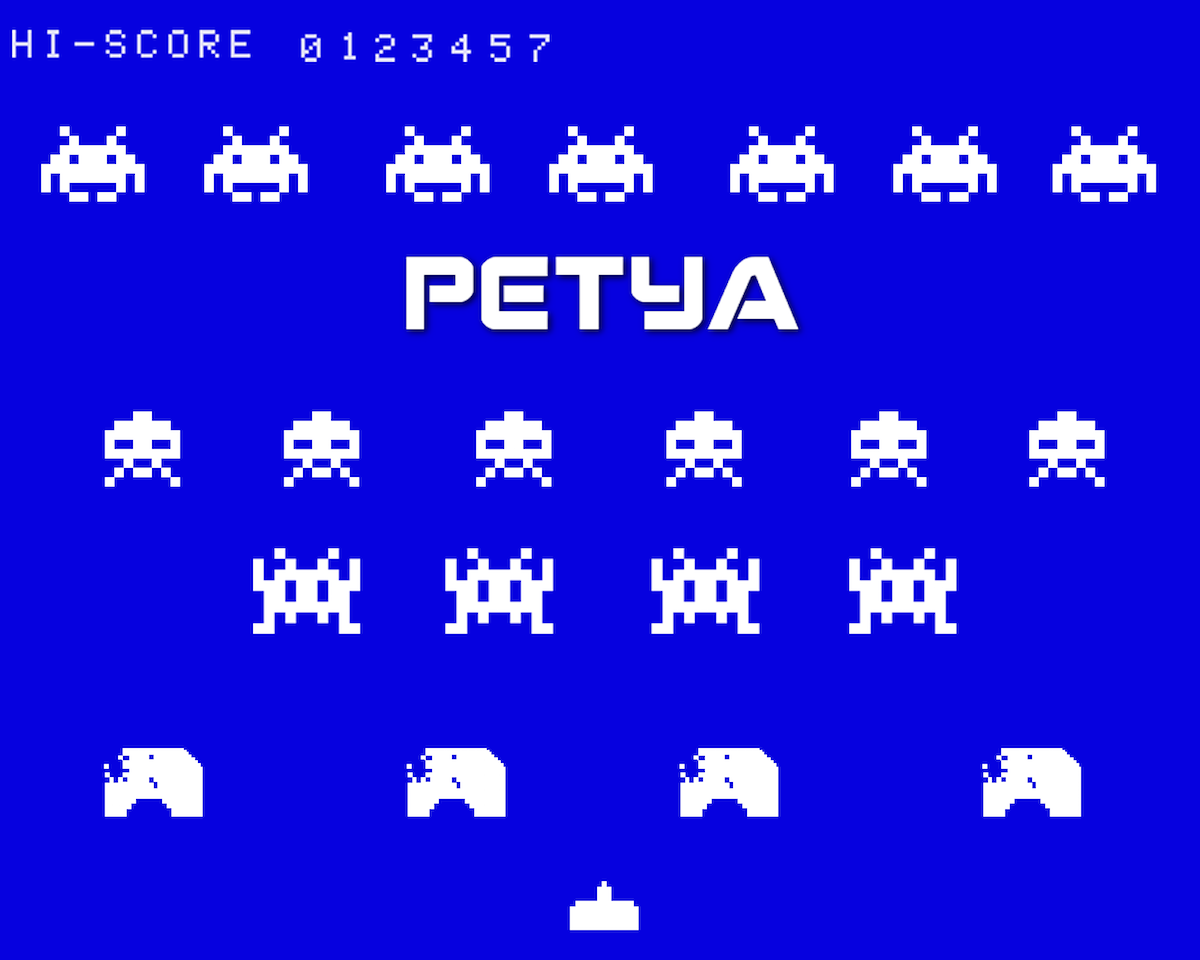
Late last month, the “Petya” variant (following May’s “Wanna Cry” attack) hit several different countries, including Ukraine, Denmark, India, Great Britain, the United States, and Russia. The nefarious code locked down vital operating systems, sealed private data, and demanded a $300 bitcoin payment to release the files. Yes, Bitcoin, the untraceable virtual digital currency, the favored stash vehicle for illicit transactions.
The sudden rise of ransomware should keep you up at night because this insidious form of digital blackmail can wreck your work or life in an instant. Blackmailers don’t suddenly reel back their threats out of the goodness of their heart. Indeed, there’s no guarantee that paying the ransom will even release your system from the hacker’s control, making repeat ransoms likely.
The list of Petya victims is long: Maersk, the sprawling Danish energy and transportation company, Rosneft, a Russian oil firm, DLA Piper, a global law firm headquartered in London, and WPP, a major British advertising and PR firm. By far the greatest number of victims have been in Ukraine – from the National Bank, to the airport, and even Chernobyl’s radiation monitoring system.
The underlying code is deadly, utilizing the NSA’s EternalBlue exploit, stolen in April by the Shadow Brokers cracker gang. Released online, these hacking tools are a veritable Pandora’s Box for any entity to utilize and exploit.
Rule number one in the hazy, mysterious world of hacking is that appearances can be deceiving. The ransomware factor in Petya has failed to extract much cash, and many of those who paid up have found their files already deleted. Experts have postulated that the “ransom” element was simply a devious cover for a nation state attack on Ukraine, especially since the infections seemed to “specifically target Ukraine’s most vital institutions, rather than making a broader attempt to find lucrative ransomware targets.”
There’s another reason to believe Ukraine was the target. The Financial Times has reported that it was a sophisticated, two-step intrusion: hackers first penetrated a Ukrainian accounting software firm and “hijacked a legitimate software update” sent to numerous Ukranian business and government departments” to then infect them with Petya. Western experts and Ukranian security professionals say the recent attack is likely just the latest Russian broadside in its ongoing military actions in Ukraine. The past is a strong clue: Ukraine, a buffer between Russia and NATO countries, has been a regular testing ground for Russian cyberattacks that spark frequent blackouts and other infrastructure failures.
Trump’s bizarre suggestion this weekend that the US should partner with Moscow on a cybersecurity unit was widely mocked by Republicans and Democrats alike. “I am sure that Vladimir Putin could be of enormous assistance in that effort, since he’s doing the hacking,” Senator John McCain, Republican of Arizona and the chairman of the Armed Services Committee, said on CBS’s “Face the Nation.”
The frightening reality is that Petya has already extracted a heavy price on its victims, paralyzing airports, banks, and energy firms. Meanwhile, the virus has spread to over 65 countries, and continues to disable vital IT frameworks, causing panic and disorder. The risks are huge. Disable a power grid’s computers, and it’s like pulling the plug on a city, causing traffic mayhem and bringing essential business to a halt. Hospital system shutdowns endanger hundreds of patients on life support.
These are weapons of mass technological destruction, and it’s only going to get worse. Whatever the origins of this particular malware, the proliferation of IoT technologies and automation is making cybersecurity more vital than ever. Creating valid contingency plans to combat and quarantine infected systems will become a do-or-die priority for businesses and individuals.
How To Stay Protected?
Microsoft, Apple, and other tech companies work around the clock to ensure that their products are secure and protected. Their solutions are not foolproof, of course, but we can minimize our chances of infection by following a few best practices.
One of the worst things you can do is to own an unsupported version of your OS. Whether from lack of funds or technological skills, an estimated 7% of Windows users are still running the 12-year-old Windows XP OS. Support for this antiquated system was officially discontinued by Microsoft in 2014, yet millions of personal and enterprise customers are foolishly continuing to run their systems on it. Incredibly, the UK’s Metropolitan Police Service stubbornly persists in running the outdated OS on at least 18,000 computers. Microsoft has recently released a custom patch for Windows XP to cover this vulnerability, but strongly encourages its customers to upgrade to a supported version: Windows 7, 8, or 10.
Beware of Strangers
Play it smart. Do not access any suspicious files or links from unknown email senders or websites. Malware may even be disguised as an email from a coworker or a friend, forwarding you a “report” or other file demanding your attention. You’ve got to be cautious about opening emails, since your spam filter won’t always catch things that seem to be from trusted sources. Many companies now require their employees to complete an annual phishing awareness test.
Another guard against malware is to create frequent backups. This is your fail-safe. You have the option of storing backups locally, cloud servers, and even networked drives. Even if your system becomes infected and irrecoverable, you can still rebuild with a recent clean backup. To provide a robust safety net make sure that your storage devices are not connected to your network after the backup is made. Testing the recovery process is equally vital. Stephen Cobb, senior security researcher at IT security company ESET, says: “The biggest gotcha that companies are encountering when they get hit with ransomware is that they haven’t had a recent test of their recovery process.”
Ultimately, the best way to combat a cyberattack is to prevent infection in the first place. Check frequently for new security updates. Use a trusted antivirus software on all systems. Lastly, don’t access suspicious websites or files. According to the National Cyber Security Centre, having good “access control” can limit potential infection to only the local user.
With attacks likely to become more frequent and more automated, there’s a simple truth that many companies, institutions and users need to wrap their head around. Pay now for the latest software, hardware, and invest in the time and diligence required to stay on top of installing frequent updates.
Or pay later with your data and your livelihood.
Curious about Fake News and Russian Bots? Check out Eric’s other story:
Following the Bots connecting Jared Kushner to all things digital and Russian?


